Breadcrumb
A New Scheme for Ransomware Classification and Clustering Using Static Features
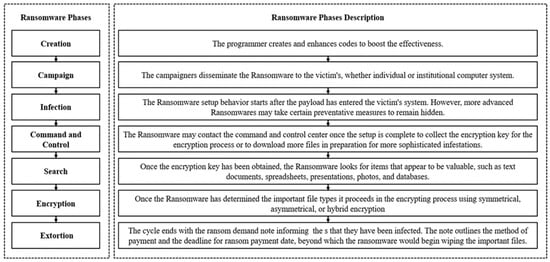
Ransomware is a strain of malware that disables access to the user’s resources after infiltrating a victim’s system. Ransomware is one of the most dangerous malware organizations face by blocking data access or publishing private data over the internet. The major challenge of any entity is how to decrypt the files encrypted by ransomware. Ransomware’s binary analysis can provide a means to characterize the relationships between different features used by ransomware families to track the ransomware encryption mechanism routine. In this paper, we compare the different ransomware detection
An Evaluation of Time Series-Based Modeling and Forecasting of Infectious Diseases Progression using Statistical Versus Compartmental Methods
As a case study for our research, COVID-19, that was caused by a unique coronavirus, has substantially affected the globe, not only in terms of healthcare, but also in terms of economics, education, transportation, and politics. Predicting the pandemic's course is critical to combating and tracking its spread. The objective of our study is to evaluate, optimize and fine-Tune state of the art prediction models in order to enhance its performance and to automate its function as possible. Therefore, a comparison between statistical versus compartmental methods for time series-based modeling and
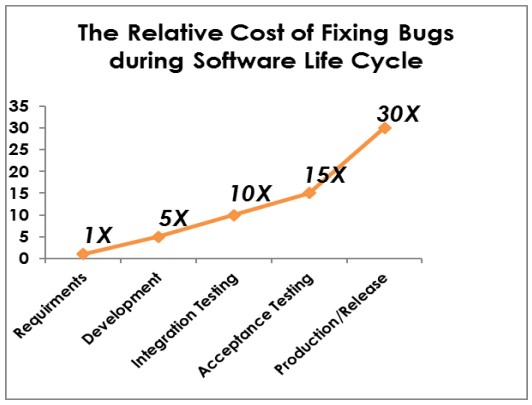
Evaluation of Software Static Analyzers
With the massive increase of software applications and websites, testing has become a very important concern in the software development process. This is due to the spread of a large number of security flaws. Dynamic testing requires code execution to examine the functional and non-functional behavior of software systems. It requires more time and cost, and it finds fewer bugs. On the other hand, static testing is done before code deployment and without code execution. Additionally, it provides a comprehensive diagnostics of code and focuses more on defects prevention. This provides greater
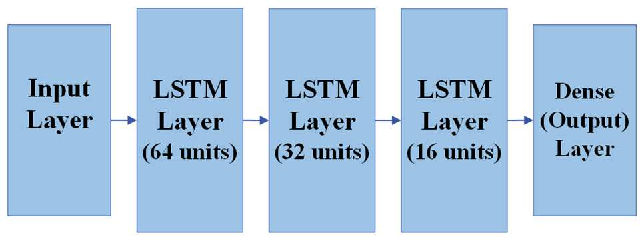
Multi-Band Radio Frequency Energy Predictor for Advanced Energy Harvesting Cellular Bands Systems
Radio Frequency (RF) energy harvesting has been employed to power wireless devices. Nevertheless, RF energy harvesting encounters restrictions regarding the quantity of power it can harvest depending on signal accessibility. As a result, accurately predicting energy levels becomes crucial for enhancing the performance of energy harvesting circuits. Most research efforts have concentrated on enhancing power harvesting policies or theoretically estimating the energy obtained through RF energy harvesting. Moreover, the existing literature has primarily focused on single-band prediction approaches
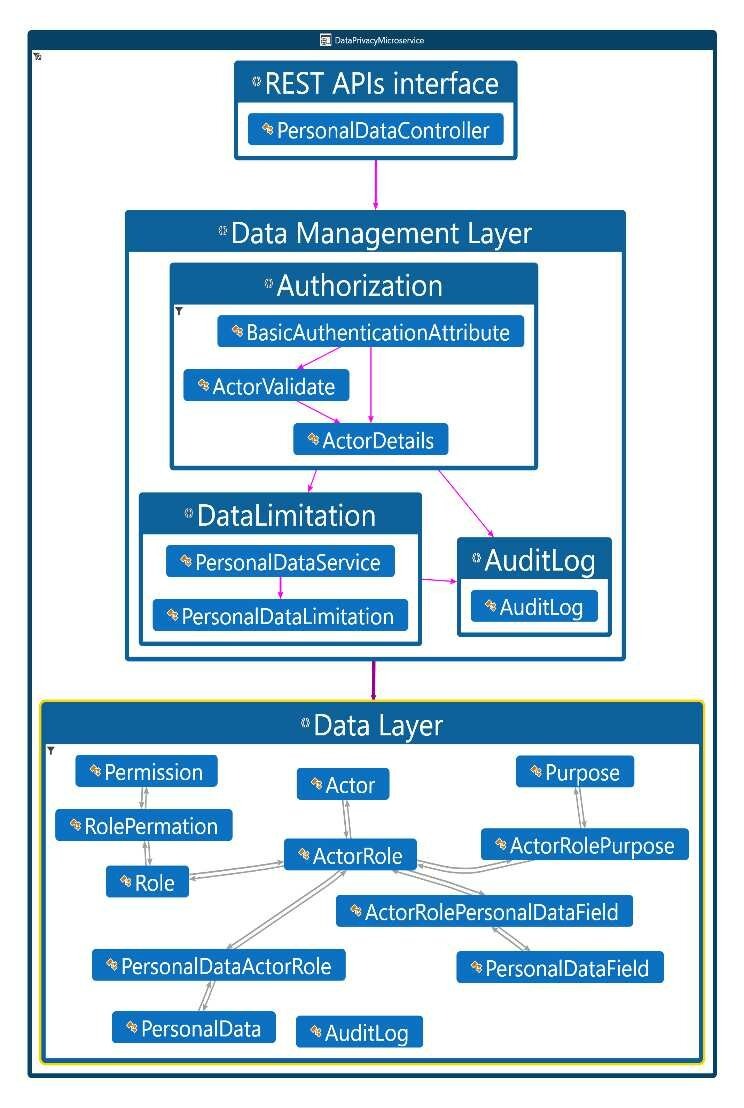
Privacy by Design: A Microservices-Based Software Architecture Approach
Data privacy regulations have increased significantly recently. As a result, privacy by design (PbD) has become a critical consideration for enterprises that handle personal data. PbD is no longer a plain principle. Rather than that, the General Data Protection Regulation (GDPR) addresses PbD as a required legal requirement for controllers who may face fines for non-compliance with the GDPR. In this paper, we propose a practical solution, 'PbD Microservice,' that can help organizations to achieve privacy regulatory compliance. We will focus on GDPR, one of the most important regulations that
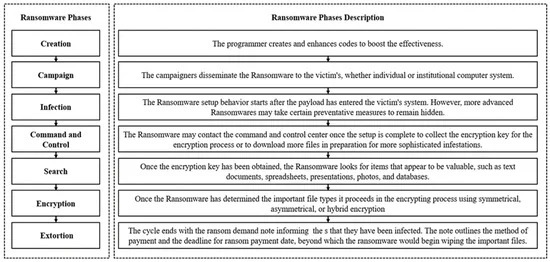
Ransomware Clustering and Classification using Similarity Matrix
Ransomwares are amongst the most dangerous malwares that face and affect any business by restricting data access or leaking sensitive information over the internet. Ransomwares binary analysis can provide a way to define the relationships between distinct features employed by ransomware families. Malware classification and clustering systems offer an effective malware indexing with search functionalities, similarity checking, samples classification and clustering. Most studies focus on the static and dynamic features extraction, machine and deep learning or visualization techniques used to

Penetration Testing: A Cost-Benefit Analysis of Best Practices Implementation for Software Startups
Despite software startups often not handlingsensitive data, the implementation of robust security measures is crucial to mitigate significant financial and reputational risks. This study investigates the cost-benefit analysis of implementing best practices in penetration testing (Pentest) versus notimplementing them, using Roboost as a case study. It emphasizes that proactive security investments not only protect current assets but also prepare organizations for future growthThe research employs a mixed-methods approach, combining quantitative analysis of financial data with qualitative
Improving the Performance of Semantic Text Similarity Tasks on Short Text Pairs
Training semantic similarity model to detect duplicate text pairs is a challenging task as almost all of datasets are imbalanced, by data nature positive samples are fewer than negative samples, this issue can easily lead to model bias. Using traditional pairwise loss functions like pairwise binary cross entropy or Contrastive loss on imbalanced data may lead to model bias, however triplet loss showed improved performance compared to other loss functions. In triplet loss-based models data is fed to the model as follow: Anchor sentence, positive sentence and negative sentence. The original data
Comparative Analysis of a Generalized Heart Localization Model: Assessing Its Efficacy Against Specialized Models
Heart localization holds significant importance in the process of the diagnosis and treatment of heart diseases. Additionally, it plays an important role in planning the cardiac scanning protocol. This research focuses on heart localization by employing the multi-label classification task with the utilization of RES-Net50. The primary objective is to predict the slices containing the heart and determine its endpoint. To ensure high-quality data, we implement filtering techniques and perform up-sampling during the pre-processing stage. Two experiments were conducted to assess different
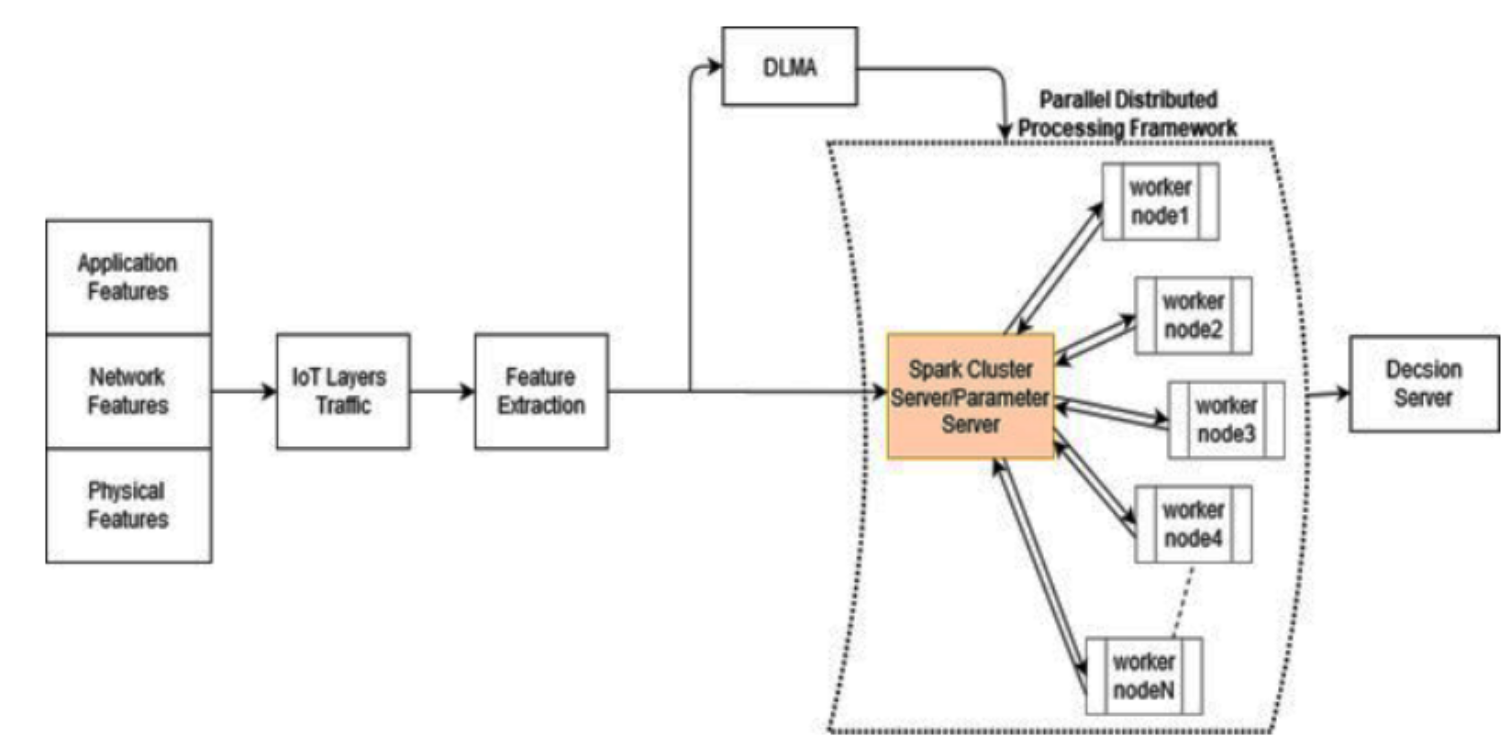
Cross-Layer Distributed Attack Detection Model for the IoT
The security of IoT that is based on layered approaches has shortcomings such as the redundancy, inflexibility, and inefficiently of security solutions. There are many harmful attacks in IoT networks such as DoS and DDoS attacks, which can compromise the IoT architecture in all layers. Consequently, cross layer approach is proposed as an effective and practical security defending mechanism. Cross-layer distributed attack detection model (CLDAD) is proposed to enhance security solutions for IoT environments. CLDAD presents a general detection method of DDoS in sensing layer, network layer, and
Pagination
- Previous page ‹‹
- Page 13
- Next page ››
