Breadcrumb
Walk Through Event Stream Processing Architecture, Use Cases and Frameworks Survey
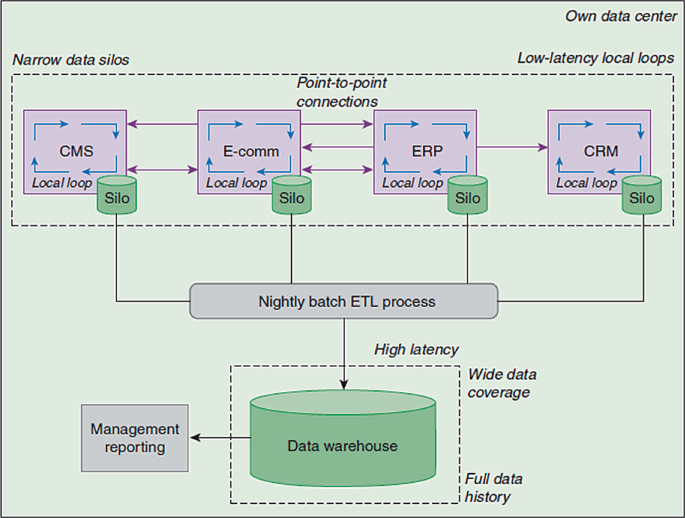
Nowadays events stream processing is one of the top demanding field(s) because of the business urgent need for ongoing real time analytics & decisions. Most business domains avail huge amount of data aiming to make use of each data point efficiently. Corporate(s) have a cloud of events vary from internal business transactions, social media feeds, IoT devices logs,.. etc. In this paper we would discuss state of the art event stream processing technologies using cloud of events by summarizing event stream processing definition, data flow architectures, common use cases, frameworks and
Sentiment Analysis for Arabic Product Reviews using LLMs and Knowledge Graphs
The exploration of sentiment analysis in multilingual contexts, particularly through the integration of deep learning techniques and knowledge graphs, represents a significant advance in language processing research. This study specifically concentrates on the Arabic language, addressing the challenges presented by its morphological complexity. While the primary focus is Arabic, the research also includes a comprehensive review of related work in other languages such as Bangla and Chinese. This contextualizes the challenges and solutions found in Arabic sentiment analysis within a broader
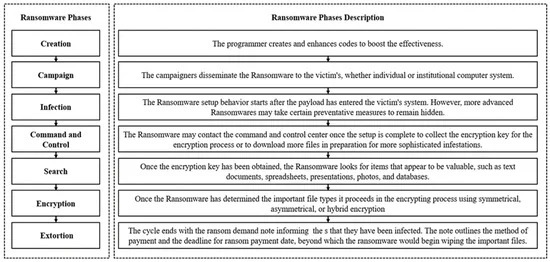
Ransomware Clustering and Classification using Similarity Matrix
Ransomwares are amongst the most dangerous malwares that face and affect any business by restricting data access or leaking sensitive information over the internet. Ransomwares binary analysis can provide a way to define the relationships between distinct features employed by ransomware families. Malware classification and clustering systems offer an effective malware indexing with search functionalities, similarity checking, samples classification and clustering. Most studies focus on the static and dynamic features extraction, machine and deep learning or visualization techniques used to

Penetration Testing: A Cost-Benefit Analysis of Best Practices Implementation for Software Startups
Despite software startups often not handlingsensitive data, the implementation of robust security measures is crucial to mitigate significant financial and reputational risks. This study investigates the cost-benefit analysis of implementing best practices in penetration testing (Pentest) versus notimplementing them, using Roboost as a case study. It emphasizes that proactive security investments not only protect current assets but also prepare organizations for future growthThe research employs a mixed-methods approach, combining quantitative analysis of financial data with qualitative
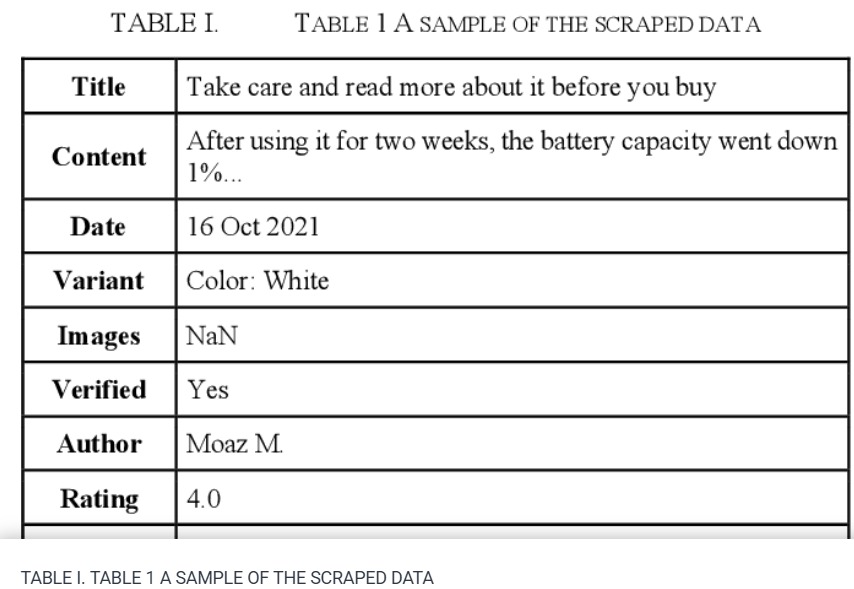
Sentiment Analysis: Amazon Electronics Reviews Using BERT and Textblob
The market needs a deeper and more comprehensive grasp of its insight, where the analytics world and methodologies such as 'Sentiment Analysis' come in. These methods can assist people especially 'business owners' in gaining live insights into their businesses and determining wheatear customers are satisfied or not. This paper plans to provide indicators by gathering real world Amazon reviews from Egyptian customers. By applying both Bidirectional Encoder Representations from Transformers 'Bert' and 'Text Blob' sentiment analysis methods. The processes shall determine the overall satisfaction
Smart Automotive Diagnostic and Performance Analysis Using Blockchain Technology
The automotive industry currently is seeking to increase remote connectivity to a vehicle, which creates a high demand to implement a secure way of connecting vehicles, as well as verifying and storing their data in a trusted way. Furthermore, much information must be leaked in order to correctly diagnose the vehicle and determine when or how to remotely update it. In this context, we propose a Blockchain-based, fully automated remote vehicle diagnosis system. The proposed system provides a secure and trusted way of storing and verifying vehicle data and analyzing their performance in
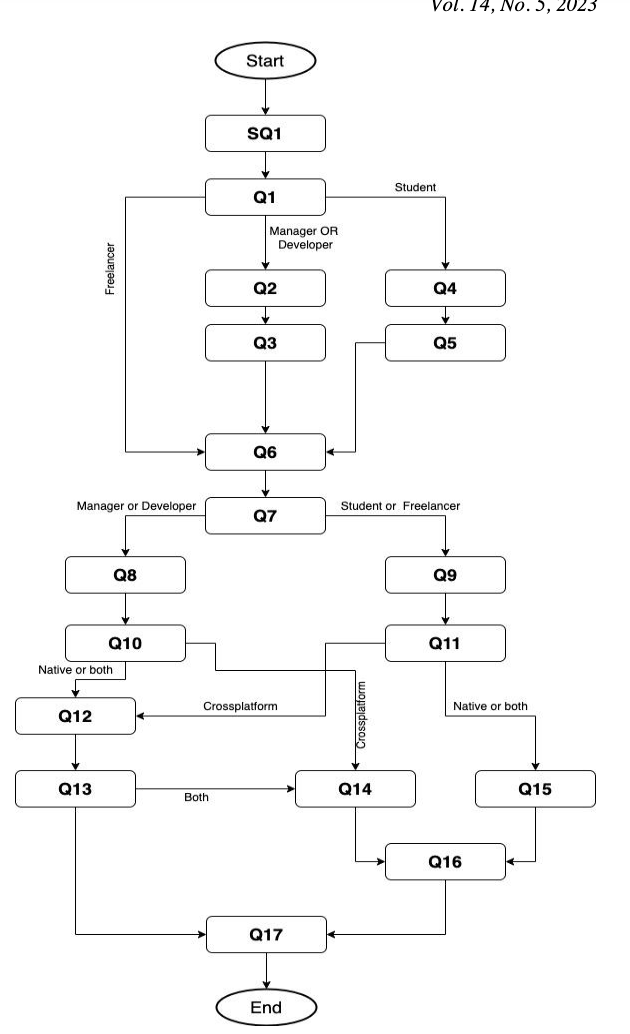
Industrial Practitioner Perspective of Mobile Applications Programming Languages and Systems
The growth of mobile application development industry made it crucial for researchers to study the industry practices of choosing mobile applications programming languages, systems, and tools. With the increased attention of cross-platform mobile applications development from both researchers and industry, this paper aims at answering the question of whether most of the industries are using cross-platform development or native development. The paper collects feedback about industry’s most used mobile development systems. In addition, it provides a map of the different technologies used by
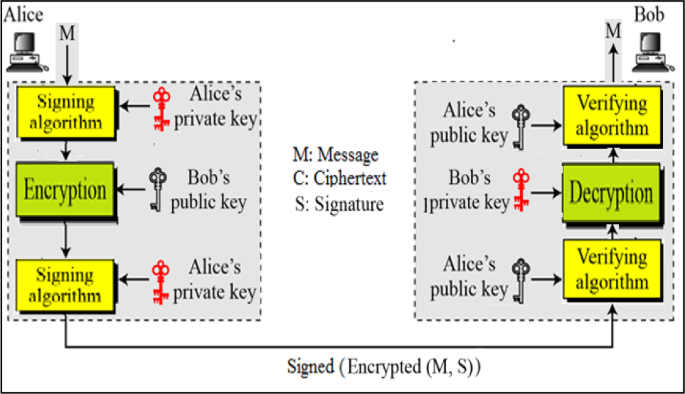
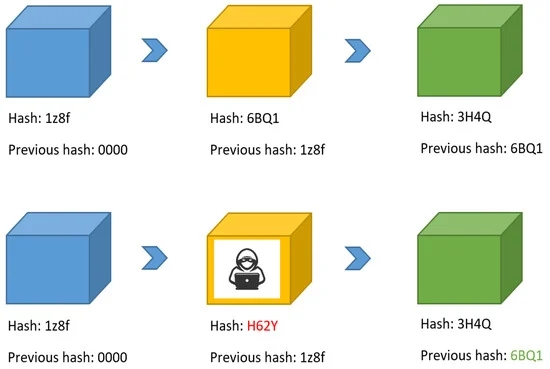
Networking and cryptography library with a non-repudiation flavor for blockchain
Blockchain is currently one of the most widely discussed inventions in the information and communication technology industry. It is a pillar of the fourth industrial revolution and it is a cryptographically demanding technology that is regarded as one of the most influential topics in academia. Many blockchain platforms currently utilize third-party cryptographic libraries that offer many cryptographic primitives in order to ensure users' protection against cyber-attacks. The Networking and Cryptography library (NaCl) is an open-source library for cryptographic primitives. NaCl is known to be
Customer Churn Prediction Using Apriori Algorithm and Ensemble Learning
Customer churn poses a formidable challenge within the Telecom industry, as it can result in significant revenue losses. In this research, we conducted an extensive study aimed at developing a viable customer churn prediction method. Our method utilizes the Apriori algorithm's strength to identify the key causes of customer churn. In the pursuit of this goal, we utilized multiple machine learning predictive models. All of which were developed from the insights gleaned from the Apriori algorithm's feature extraction for churning customers. This extensive analysis encompassed a spectrum of
Providing a labeled statements dataset to enhance the trans-compilation-based tools
Nowadays Mobile Applications are a necessity as everyone is depending on them in their everyday tasks. We use them for communication, entertainment, and utilities. Every day new devices are introduced to the market. The diversity in these devices resulted in many platforms like Android and iOS. These different mobile platforms used by different companies and manufacturers made it challenging for mobile developersto build an application or a system that can be deployed on different platforms. Developers will be required to go through multiple development cycles to develop the application for
Pagination
- Previous page ‹‹
- Page 3
- Next page ››
